If you cannot open your images, documents, or files and they have a “.rote” extension, then your computer is infected with the STOP/DJVU ransomware.
The STOP/DJVU ransomware encrypts the personal documents found on the victim’s computer, then displays a message which offers to decrypt the data if payment in Bitcoin is made. The instructions are placed on the victim’s desktop in the _readme.txt file.

- 1. What is the Rote ransomware?
- 2. How did the Rote ransomware get on my computer?
- 3. Is my computer infected with the Rote ransomware?
- 4. How to remove the Rote ransomware and recover the files
1. What is the Rote ransomware?
Rote is a file-encrypting ransomware infection that restricts access to data (files, images, videos) by encrypting files with the “.rote” extension. It then attempts to extort money from victims by asking for “ransom”, in the form of Bitcoin cryptocurrency, in exchange for access to data.
This ransomware targets all versions of Windows including Windows 7, Windows 8.1 and Windows 10. When this ransomware is first installed on a computer it will create a random named executable in the %AppData% or %LocalAppData% folder. This executable will be launched and begin to scan all the drive letters on your computer for data files to encrypt.
STOP/DJVU ransomware searches for files with certain file extensions to encrypt. The files it encrypts include important productivity documents and files such as .doc, .docx, .xls, .pdf, among others. When these files are detected, this infection will change the extension to Rote, so they are no longer able to be opened.
The STOP/DJVU ransomware changes the name of each encrypted file to the following format: name.rote
Once your files are encrypted with the “.rote” extension, you cannot open these files and this ransomware will create the info.txt ransom note in each folder that a file has been encrypted and on the Windows desktop.
When the infection has finished scanning your computer it will also delete all of the Shadow Volume Copies that are on the affected computer. It does this so that you cannot use the shadow volume copies to restore your encrypted files.
2. How did the Rote ransomware get on my computer?
The Rote ransomware is distributed via spam email containing infected attachments or by exploiting vulnerabilities in the operating system and installed programs.
Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link inside the email). And with that, your computer is infected with the Rote ransomware.
This ransomware was also observed attacking victims by hacking open Remote Desktop Services (RDP) ports. The attackers scan for the systems running RDP and then attempt to brute force the password for the systems.
3. Is my computer infected with Rote Ransomware?
Here is a short summary for the Rote ransomware:
- Ransomware family: STOP/DJVU ransomware
- Extensions: .rote
- Ransomware note: _readme.txt
- Ransom: From $490 to $980 (in Bitcoins)
- Contact: restorefiles@firemail.cc or gorentos@bitmessage.ch
- Symptoms: Your files have a .rote extension and cannot be opened by any programs
When this ransomware infects your computer it will scan all the drive letters for targeted file types, encrypt them, and then append the “.rote” extension to them. Once these files are encrypted, they will no longer able to be opened by your normal programs. When this ransomware has finished encrypting the victim’s files, it will also display a ransom note that includes instructions on how to contact these cybercriminals (restorefiles@firemail.cc or gorentos@bitmessage.ch).
This is the message that the Rote ransomware (_readme.txt) will display:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-IbdGyCKhdr
... of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
restorefiles@firemail.ccReserve e-mail address to contact us:
gorentos@bitmessage.ch
If your computer is infected with this ransomware, we recommend that you contact the following government fraud and scam sites to report this attack:
- In the United States, go to the On Guard Online website.
- In Australia, go to the SCAMwatch website.
- In Canada, go to the Canadian Anti-Fraud Centre.
- In France, go to the Agence nationale de la sécurité des systèmes d’information
- In Germany, go to the Bundesamt für Sicherheit in der Informationstechnik website.
- In Ireland, go to the An Garda Síochána website.
- In New Zealand, go to the Consumer Affairs Scams website.
- In the United Kingdom, go to the Action Fraud website.
If your country or region isn’t listed here, we recommend that you contact your country or region’s federal police or communications authority.
4. How to remove the Rote ransomware and recover the files
It’s important to understand that by starting the removal process you risk losing your files, as we cannot guarantee that you will be able to recover them. Your files may be permanently compromised when trying to remove this infection or trying to recover the encrypted documents. We cannot be held responsible for losing your files or documents during this removal process.
This guide was written to help you remove the infection itself from your computer, and if a 100% proven method to recover the encrypted files is found we will update this guide.
STEP 1: Use Malwarebytes Free to remove Rote ransomware
Malwarebytes Free is one of the most popular and most used anti-malware software for Windows, and for good reasons. It is able to destroy many types of malware that other software tends to miss, without costing you absolutely nothing. When it comes to cleaning up an infected device, Malwarebytes has always been free and we recommend it as an essential tool in the fight against malware.
- Download Malwarebytes Free.
You can download Malwarebytes by clicking the link below.
 MALWAREBYTES DOWNLOAD LINK
MALWAREBYTES DOWNLOAD LINK
(The above link will open a new page from where you can download Malwarebytes) - Double-click on the Malwarebytes setup file.
When Malwarebytes has finished downloading, double-click on the MBSetup file to install Malwarebytes on your computer. In most cases, downloaded files are saved to the Downloads folder.
 You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the Malwarebytes installation.
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the Malwarebytes installation.
- Follow the on-screen prompts to install Malwarebytes.
When the Malwarebytes installation begins, you will see the Malwarebytes setup wizard which will guide you through the installation process. The Malwarebytes installer will first ask you on what type of computer are you installing this program, click either Personal Computer or Work Computer.

On the next screen, click “Install” to install Malwarebytes on your computer.

When your Malwarebytes installation completes, the program opens to the Welcome to Malwarebytes screen. Click the “Get started” button.
- Select “Use Malwarebytes Free”.
After installing Malwarebytes, you’ll be prompted to select between the Free and the Premium version. The Malwarebytes Premium edition includes preventative tools like real-time scanning and ransomware protection, however, we will use the Free version to clean up the computer.
Click on “Use Malwarebytes Free“.
- Click on “Scan”.
To scan your computer with Malwarebytes, click on the “Scan” button. Malwarebytes will automatically update the antivirus database and start scanning your computer for malware.

- Wait for the Malwarebytes scan to complete.
Malwarebytes will scan your computer for adware and other malicious programs. This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.

- Click on “Quarantine”.
When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected. To remove the malicious programs that Malwarebytes has found, click on the “Quarantine” button.

- Restart computer.
Malwarebytes will now remove all the malicious files and registry keys that it has found. To complete the malware removal process, Malwarebytes may ask you to restart your computer.

- When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 2: Use Emsisoft Emergency Kit to scan for malware and unwanted programs
Emsisoft Emergency Kit is a free second opinion scanner that can be used without installation to scan and clean infected computers. Emsisoft scans the behavior of active files and also files in locations where malware normally resides for suspicious activity.
- Download Emsisoft Emergency Kit.
You can download Emsisoft Emergency Kit by clicking the link below.
 EMSISOFT EMERGENCY KIT DOWNLOAD LINK
EMSISOFT EMERGENCY KIT DOWNLOAD LINK
(The above link will open a new web page from where you can download Emsisoft Emergency Kit) - Install Emsisoft Emergency Kit.
Double-click on the EmsisoftEmergencyKit setup file to start the installation process, then click on the “Install” button.

- Start Emsisoft Emergency Kit.
On your desktop the “EEK” folder (C:\EEK) should now be open. To start Emsisoft, click on the “Start Emsisoft Emergency Kit” file to open this program.

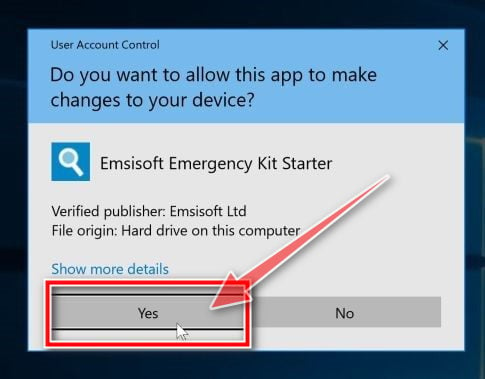
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- Click on “Malware Scan”.
Emsisoft Emergency Kit will start and it will ask you for permission to update itself. Once the update process is complete, click on the “Scan” tab, and perform a “Malware Scan“.

- Emsisoft Emergency Kit will now scan your PC for malicious files. This process can take a few minutes.

- Click on “Quarantine selected”.
When the Emsisoft scan has finished, you will be presented with a screen reporting which malicious files were detected on your computer. To remove the malicious programs, click on the “Quarantine selected“.

- When the malware removal process is complete, Emsisoft Emergency Kit may need to restart your computer. Click on the “Restart” button to restart your computer.
When the process is complete, you can close Emsisoft and continue with the rest of the instructions.
STEP 3: Restore the files encrypted by Rote ransomware with Emsisoft Decryptor for STOP Djvu
Unfortunately, in most cases, it’s not possible to recover the files encrypted by this ransomware because the private key which is needed to unlock the encrypted files is only available through the cybercriminals.
However, if your files were encrypted with an offline key there is a chance you can recover them by using Emsisoft Decryptor for STOP Djvu decryption tool.
Here’s how to recover your files using the Emsisoft Decryptor for STOP Djvu.
Make sure you remove the malware from your system first, otherwise, it will repeatedly lock your system or encrypt files.
- Download Emsisoft Decryptor for STOP Djvu
You can download Emsisoft Decryptor for STOP Djvu by clicking the link below.
 EMSISOFT DECRYPTOR FOR STOP DJVU DOWNLOAD LINK
EMSISOFT DECRYPTOR FOR STOP DJVU DOWNLOAD LINK
(The above link will open a new web page from where you can download Emsisoft Decryptor for STOP Djvu) - Run Emsisoft Decryptor for STOP Djvu
When Emsisoft Decryptor for STOP Djvu has finished downloading, double-click on “decrypt_STOPDjvu.exe” to run this program on your computer. In most cases, downloaded files are saved to the Downloads folder.

You may be presented with a User Account Control pop-up asking if you want to allow Emsisoft to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- Follow the on-screen prompts
When the Emsisoft Decryptor for STOP Djvu starts, you will need to agree with the Terms and accept a disclaimer.

- Click on “Decrypt”.
Click the “Decrypt” button to start the decryption process. The screen will switch to a status view, informing you about the current process and decryption status of your files.

- The decryptor will inform you once the decryption process is finished. If you require the report for your personal records, you can save it by clicking the “Save log” button. If your system was compromised through the Windows Remote Desktop feature, we also recommend changing all passwords of all users that are allowed to login remotely and check the local user accounts for additional accounts the attacker might have added.
Unfortunately, in most cases, it’s not possible to recover the files encrypted by the Rote ransomware because the private key which is needed to unlock the encrypted files is only available through the cybercriminals.
Do not pay any money to recover your files. Even if you were to pay the ransom, there is no guarantee that you will regain access to your files.
Your computer should now be free of the Rote ransomware infection. If your current antivirus allowed this malicious program on your computer, you may want to consider purchasing the full-featured version of Malwarebytes Anti-Malware to protect against these types of threats in the future.


